Huawei NIP6000 Next Generation Intrution
Prevention System
Huawei’s NIP6000 series is an advanced intrusion prevention
system designed to provide application and service security for
enterprises, IDCs, campus networks, and carriers.
The NIP6000 series utilizes context, application, and content
awareness to defend against unknown threats by implementing accurate
detection and optimized management. For customers, application and
security measures ensure comprehensive protection of valuable
network infrastructures, servers, clients, and bandwidth
performance.

Product Highlights
New hardware and software architecture, providing
industryleading performance
- Uses a dedicated multi-core and multi-CPU platform, which greatly
improves detection performance.
- Provides dedicated hardware for decompression and pattern matching
to ensure high traffic processing efficiency and optimal performance
with multi-level protection.
- Uses a new intelligent awareness engine (IAE) for threat detection,
which enables multi-level protection and concurrent processing and
improves threat detection efficiency.
Multi-level detection for comprehensive protection
- Protects operating systems and applications from malware and
attacks.
- Identifies more than 120 types of files, prevents file name
extension tampering, and identifies malicious code in files.
- Provides superior anti-DDoS capabilities to mitigate
application-layerDDoS attacks (such as HTTP, DNS, and SIP attacks).
- Implements SSL encryption and advanced evasion detection.
- Detects unauthorized connections to servers and protects information
assets.
Dynamic context awareness for intelligent policy tuning
and hierarchical log management
- Identifies security risks to both static assets and dynamic traffic.
- Automatically tunes security policies based on the security risks.
- Analyzes the detection logs based on the security risks for
hierarchical log management.
Interworking with the sandbox and reputation systems for
threat detection
- Interworks with the sandbox for suspect file analysis and ther at
file detection.
- Interworks with the IP and C&C reputation systems for rapid threat
detection and prevention.
Fast signature update for prompt vulnerability protection
- Captures the latest attacks, worms, viruses, and Trojan horses,
extracts signatures from them, and determines the threat trend using
a global honeynet.
- Updates the signature database and inspection engine promptly when
new and zero-day threats and vulnerabilities are identified.
- Certified "CVE-Compatible". Threat analysis and verification are
compatible with Common Vulnerabilities and Exposures (CVE)
requirements.
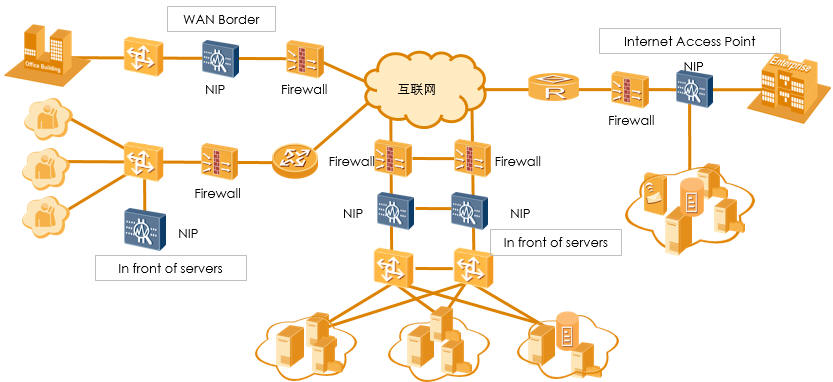
Deployment Scenarios
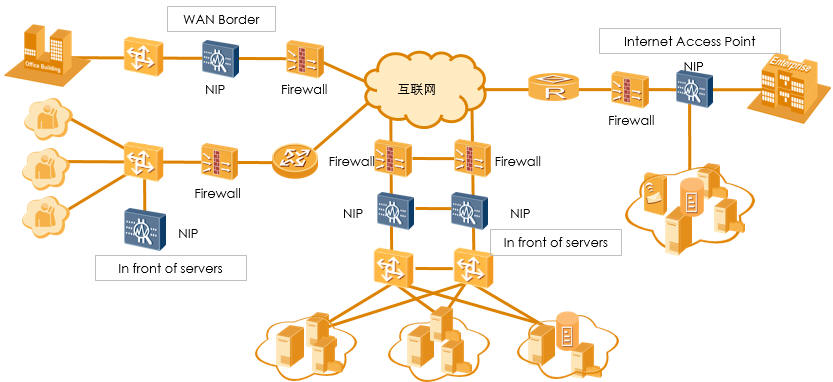
Internet access point
-
- Limits undesired P2P and video traffic and ensures the
bandwidth for proper services.
-
- Prevents IM, online gaming, and stock exchange applications
to avoid network abuse.
-
- Prevents online storage, Web mail, and IM applications to
avoid disclosure of internal documents or confidential
information.
-
- Protects internal hosts and browsers against threats to
avoid data loss, data damage, or turning the hosts into zombies
Offline Monitor (IDS mode)
-
- Meets the requirement of policy compliance.
-
- Meet the governmental mandatory standards in classified
protection of information system and secret-involved networks.
-
- Helps to maintain the network by providing key information
for intrusion detection or faults caused by other anomalies.
-
- Helps enterprises to pass standard authentications, which
are necessary for company listing or investment promotion.
In front of servers
-
- Prevents worms and exploits targeting at service and
platform vulnerabilities to avoid possible damage, tampering,
data loss, or turning the servers into zombies.
-
- Prevents server faults caused by DoS or DDoS attacks.
-
- Prevents emerging attacks, such as SQL injection, cross-site
scripting, scanning, password guessing, and sniffing, targeting
at Web applications.
-
- Provides IDC value-added services.
WAN Border
-
- Implements network logical isolation.
-
- Prevents the spread of worms and Trojan horses from external
networks.
-
- Monitors violations on internal networks.
-
- Detects and prevents malicious behaviors, such as sniffing
and reconnaissance, from external networks.
Product Specification
|
Specifications
|
NIP6330
|
NIP6610
|
NIP6620
|
NIP6650
|
NIP6680
|
|
Fixed Ports
|
8 GE + 4 SFP
|
4 GE + 2 Combo
|
8 GE + 4 SFP
|
8 GE + 4 SFP
|
4 x 10 GE + 16 GE + 8 SFP
|
Intrusion Prevention
|
- Defends against common attacks, such as worms,
Trojan horses, botnets, cross-site scripting, and SQL
injection, based on the signature database, and provides
user-defined signatures to defend against new attacks.
|
Intelligent Management
|
- Detects the types, operating systems, and enabled
services of protected IT assets; dynamically generates
suitable intrusion prevention policies for the IT
environment.
- Evaluates the risk level of attack events based on
the IT environment so that administrators can process
critical attack events and ignore false positive
attacks.
|
APT Detection
|
- Detects APT attacks based on reputation systems and
the sandbox. The NIP6300/6600 sends suspect files to the
sandbox for detection and then displays attack events
based on the sandbox detection results.
- Supports IP and C&C reputation to detect and prevent
malicious IP addresses and domain names.
|
Application Security
|
- Automatically learns traffic patterns and defends
against multiple types of DDoS attacks at the
application layer, including HTTP, HTTPS, DNS, and SIP
flood attacks.
- Scans for viruses in files transmitted through HTTP,
FTP, SMTP, POP3, IMAP, NFS, and SMB to prevent
virus-infected files from being transmitted.
- Identifies more than 6,000 applications, including
P2P, IM, online gaming, social networking, video, and
audio applications; takes action (block, traffic
limiting, application usage display) based on the
identified applications.
|
Web Security
|
- Decrypts HTTPS traffic and detects threats.
- Provides a URL blacklist to control online behavior.
|
Network Security
|
- Detects threats in VLAN, QinQ, MPLS, GRE, IPv4 over
IPv6, and IPv6 over IPv4 tunnel traffic.
- Defends against multiple types of single-packet
attacks
- Blacklists the source or destination IP addresses of
attacks to block the follow-up packets from or to the
blacklisted IP addresses.
|
High Availability
|
- Supports hot backup protocols, such as VRRP, VGMP,
and HRP; provides a hot standby mechanism to ensure that
services can automatically and smoothly switch to the
standby device if the active device fails.
|
Signature Database Update
|
- Supports online and offline updates of the IPS-SDB,
SA_SDB, and antivirus SDB for the device to have the
latest defense capabilities
|