Huawei anti-DDoS solution incorporates extensive experience in network security and full understanding of customer demands. Designed for carriers, enterprises, data centers, and ICP service providers (including Web portals, game service providers, online videos, DNS service providers, and CDN services), the solution enhances the defense capability against application-layer attacks and the attacks in IPv6-IPv4 composite networking. This fully ensures network security and service continuity
Designed for carriers, enterprises, data centers, and ICP service providers (including providers for Web portals, online games, online videos, and DNS services), Huawei anti-DDoS solution incorporates extensive experience in network security and full understanding of customer demands.
Huawei anti-DDoS solution enhances defense against application-layer attacks, IPv4-IPv6 attack defense, and defense against zombies, Trojan horses, and worms. This fully ensures network security and service continuity.
Huawei anti-DDoS solution uses the leaser-specific service design for management configuration, which implements a series of functions, including leaser service model learning, leaser configuration, and report self-service. Moreover, IDC operators can provide the anti-DDoS solution for their leasers as an SAAS service to increase the leaser viscosity, improve IDC competitiveness, and add IDC operation profits.
Service-based defense policy
Huawei anti-DDoS solution supports continuously periodic learning and analysis on the service traffic of the Zone, draws the outline of normal service traffic, and enables differentiated defense types and policies for various services or one service in different time ranges, therefore implementing refined defense.
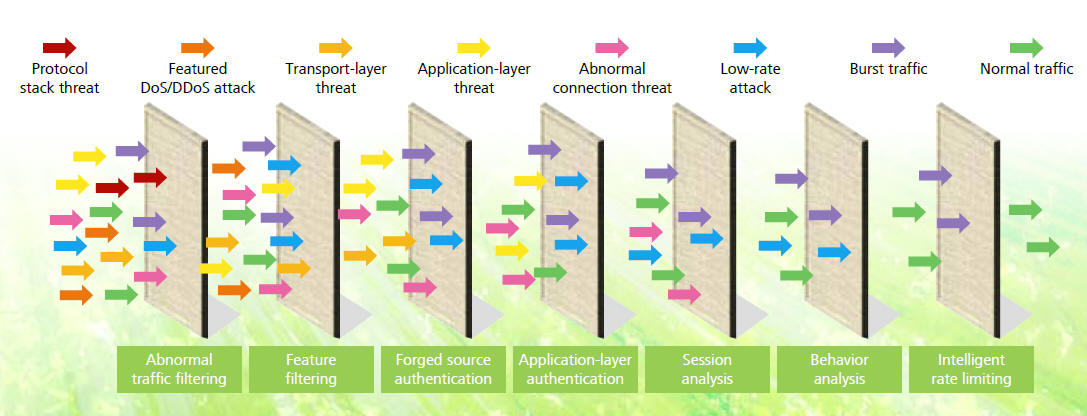
Accurate abnormal traffic cleaning
Huawei anti-DDoS solution uses the per-packet detect technology. Defense is triggered immediately by an attack. This solution applies multiple technologies, including seven-layer filtering, behavior analysis, and session monitoring, to accurately defend against various flood attacks, Web application attacks, DNS attacks, SSL DoS/DDoS attacks, and protocol stack vulnerability attacks. In this way, application servers are protected.
Intelligently caching DNS traffic
Besides accurately defending against various attacks on the DNS server, Huawei anti-DDoS solution supports DNS cache for improved performance under heavy DNS server traffic.
Defense against prevailing zombies/Trojan horses/worms
By spreading Trojan horses and worms to large numbers of hosts, hackers control the hosts hierarchically and form the botnet to launch attacks. Therefore, botnets breed DDoS attacks. Huawei anti-DDoS solution identifies and blocks over 200 common zombies/Trojan horses/worms worldwide, therefore smashing botnets.
Perfect IPv4-IPv6 defense
In February 2011, IANA declared that IPv4 addresses were exhausted. Enterprises have no new IPv4 addresses and begin to put IPv6 network construction into agenda. The particular IPv4-IPv6 technology of Huawei anti-DDoS solution supports concurrent defense against DDoS attacks on both IPv4 and IPv6 networks. The solution addresses the DDoS attack defense requirements in dual stack and helps users transit to the next generation network.
Flexible networking
The anti-DDoS solution must be adaptive to various network
environments and address different grades of service requirements.
On this basis, Huawei anti-DDoS solution provides multiple in-line
and off-line deployments, which enable customers to select
flexibly by their services and networks.
In-line deployment: serially connects the detecting and cleaning
modules to the network to be protected for direct traffic
detecting and cleaning. The high-performance and multi-core hardware
platform in use not only ensures the detecting and
cleaning accuracy, but also minimizes the processing delay.
Moreover, Huawei anti-DDoS solution provides the bypass module.
When an anomaly occurs, traffic is sent to the cleaning module,
which avoids introducing new failures.
Off-line traffic-diversion deployment: deploys the cleaning module
on the network in off-line mode. Once detecting DDoS
attack traffic, the detecting and cleaning centers perform actions
based on the policies configured in the management center.
Highlights of Huawei anti-DDoS solution:
Efficient and speedy: 200 Gbit/s defense performance and response
within seconds
High-performance and multi-core CPU, providing anti-DDoS products
covering 2 Gbit/s to • 200 Gbit/s performance to
defend against all types of DDoS attack.
• Self-learning of the service model and per-packet detect
technology. Once a traffic or packet anomaly is found, the defense
policy is automatically triggered. The defense latency is within two
seconds.
Accurate and comprehensive: "V-ISA" reputation technical system, Can
defend against hundreds of attacks
• "V-ISA" reputation technical system, Can defend against hundreds
of DDoS attacks, with the industry-leading
defense types.
• Defense against over 200 zombies, Trojan horses, and
worms, protecting users from hackers.
• IPv4/IPv6, as the first to support IPv6 attack defense and
concurrent IPv4 and IPv6 attack defense.
• Particular terminal identification technology to accurately
identify client types, such as smart terminals, set-boxes, and
common clients, as well as client-specific defense technologies to
ensure zero false positive.
Value-added operation: protection for tens of thousands of leasers
and diverse self-services
• Leaser-based service design to protect 100,000 leasers
concurrently.
• Self-configuration of defense policies and the generation of
independent security reports, providing visibility into defense
effects.
• Capture of attack packets, extraction of attack features, and
user-defined attack feature filtering to effectively defend
against DDoS attacks and zero-day attacks.
As shown in the following figure, Huawei anti-DDoS solution
comprises the detecting center, cleaning center, and ATIC
management center. By means of policy interworking and control
interworking, the three centers provide a professional anti-DDoS
solution with easy management and flexible deployment for customers.
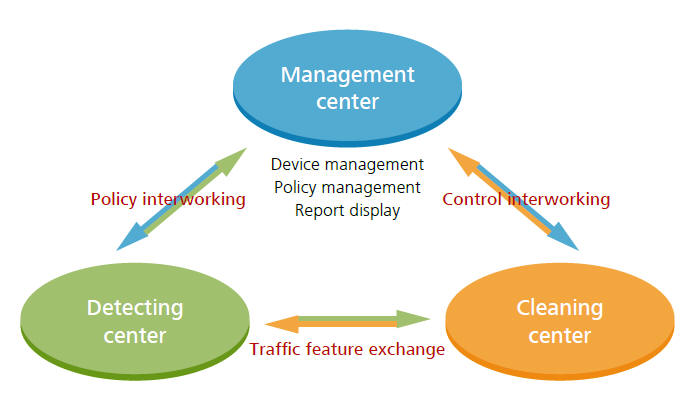
Detecting center: As the "antenna" of the entire solution, the
detecting center receives detecting policies delivered by the ATIC
management center, identities and detects DDoS traffic, and gives
detecting results back to the ATIC management center.
• Cleaning center: As the "executor" of the entire solution, the
cleaning center cleans DDoS traffic on the network based on the
control signals delivered by the ATIC management center.
• ATIC management center: As the "brain" of the solution, the ATIC
management center allows the user to customize
detecting and cleaning policies and delivers the policies to the
detecting center and cleaning center to control the detecting and
cleaning process.Meanwhile, the user can also generate and view
attack reports and cleaning records in the ATIC management center.
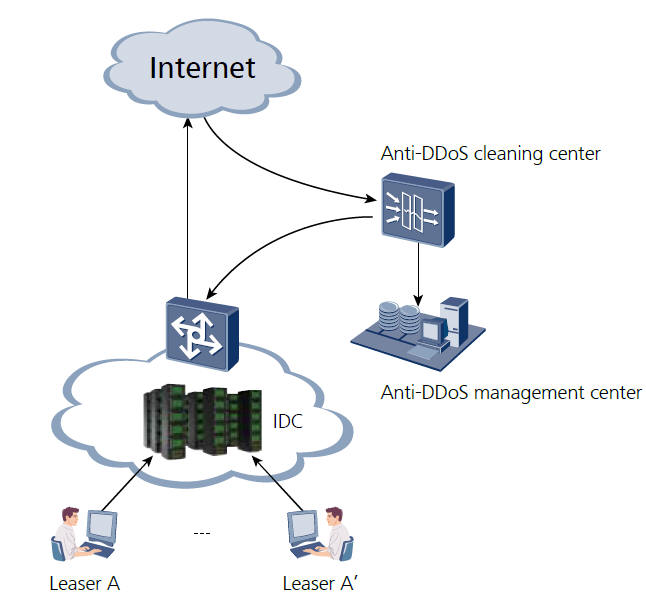
Huawei anti-DDoS solution deployed at the IDC egress delivers the
following functions:
1. Defends against attacks on the DNS server, for example, DNS
protocol stack vulnerability attacks, DNS reflection attacks, DNS
flood attacks, and DNS CacheMiss attacks, and supports DNS cache for
improved DNS server performance under heavy traffic.
2. Defends against attacks on Web servers, for example, SYN flood
attacks, HTTP flood attacks, CC attacks, and low-rate connection
attacks.
3. Defends against attacks on online games, for example, UDP flood
attacks, SYN flood attacks, and TCP attacks.
4. Defends against SSL DoS/DDoS attacks on HTTPS servers.
5. Provides customers with self-service policy configuration and
report by operating anti-DDoS as a security service.
High-performance, expandable platform providing non-stop protection against hundreds of DDoS attacks for carriers, large-scale enterprises, Internet data centers, and ISPs.

Dedicated appliances providing anti-DDoS protection for IT infrastructure and online services of enterprise networks, financial institutions, and ISPs

Contact us: Tel: 1-866-318-6636 (US/CANADA)
Email: [email protected]